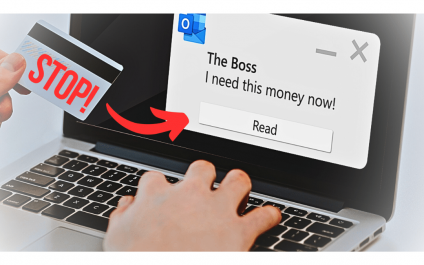
While business owners may invest heavily in malware protection, they often overlook the vulnerabilities inherent in human behavior. Social engineering, a cunning strategy that exploits human trust and psychology, requires little or no sophisticated technology, yet can inflict significant damage by luring unsuspecting individuals into divulging sensitive information. To safeguard your business from these deceptive […]
Blog
Choosing between cloud and on-premises VoIP? Consider these first

The choice between cloud-based and on-premises Voice over Internet Protocol (VoIP) hosting is a strategic decision that can significantly impact the efficiency and effectiveness of your business’s communication infrastructure. To make an informed choice, it’s crucial to weigh the factors that matter most to your organization, whether it’s flexibility, security, scalability, or cost-effectiveness. Let’s explore […]
Keep your company running with business continuity tactics

When it comes to business, one thing is certain: the unexpected will always find a way to disrupt your operations. Whether it’s a global pandemic, extreme weather conditions, or a cyberattack, it is essential to have measures in place that will allow your company to continue functioning during these uncertain times. A robust business continuity […]
The 5 keys to collecting customer data securely

A major aspect of business is meeting people’s wants. To understand people’s wants, businesses collect and analyze customer information. At the same time, businesses need to follow data privacy regulations. Violating these regulations can mean fines, penalties, and loss of customer trust. To avoid such consequences, you need to know the five keys to collecting […]
Best practices for remote work security

Remote work setups are here to stay, and with them comes the pressing concern of cybersecurity. As companies increasingly embrace distributed workforces, protecting sensitive data and systems has never been more crucial. This blog will guide you on how to proactively manage the security risks that come with remote work. Create clear remote work policies […]
What makes VoIP phishing cybercriminals’ weapon of choice?

Voice over Internet Protocol (VoIP) phishing, a technique that involves manipulating VoIP technology to trick users into giving up sensitive information, has become a favored tool in every cybercriminal’s arsenal. But why is this so? Let’s take a look at the reasons scammers choose this nefarious activity over other schemes. By unraveling why VoIP attacks […]
The hidden dangers of free VPNs

Are you aware that the rise in global VPN usage has skyrocketed? The reasons are clear as day: Virtual Private Networks offer increased security, anonymity, and allow access to geo-restricted content online. But here’s the million-dollar question: Are all VPNs created equal?
The answer is a resounding no.
3 ways AI makes almost any business task easier

In the fast evolving world of technology, business owners and managers like you are always on the lookout for the next big thing to give them a competitive edge.
Have you considered how AI tools might be able to help?
ChatGPT – or Generative Pretrained Transformer, if you want to get technical – has been making big waves all year.
This is the latest trend in phishing attacks

Have you heard the saying, “A picture is worth a thousand words”? It seems cybercriminals have too, and they’re using it to their advantage.
In a new twist on phishing campaigns, cybercriminals are luring victims to click on images rather than downloading malicious files or clicking suspicious links.